Surprising nobody, a new security threat has been detected out in the wild. At this rate, we'll need to hang up a sign in the office that says, "Days since last security alert..." If we left the counter at zero, I think it would be correct more often than not.
Netfilter driver communicating with Chinese-based servers
The driver in question, called "Netfilter," was detected by G Data security analyst Karsten Hahn. The Netfilter driver raised suspicion as the driver provided no valid functionality but was detected redirecting traffic to a command and control server with a Chinese IP address.
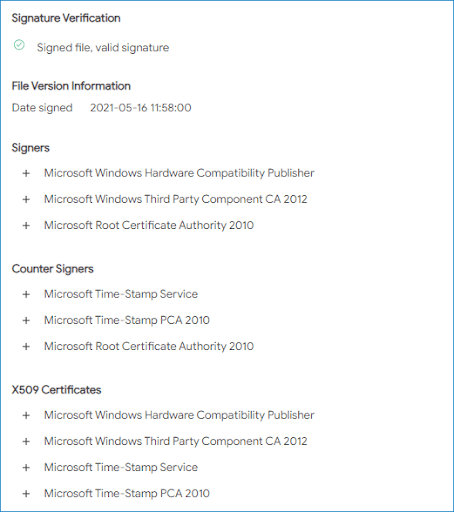
While malicious drivers are nothing new, what sets Netfilter apart is that it was verified and signed by Microsoft.
Microsoft confirms findings
Microsoft has been quick to respond to the findings, confirming that the malicious driver did contain a valid signature. Microsoft has stated that there is no evidence of stolen code-signing certificates, but that the Netfilter driver was submitted for certification through the Windows Hardware Compatibility Program (WHCP).
While it's comforting to be assured that the code-signing certificate wasn't stolen, it obviously highlights a flaw with Microsoft's code signing process that this third party was able to abuse. Microsoft has yet to identify or at least provide an explanation as to how the driver made it through their process, but that they will be sharing an update on how they are "refining our partner access policies, validation and the signing process to further enhance our protections" in the future.
In its response, Microsoft emphasized the actor's activity was limited to the "gaming sector, specifically in China, and does not appear to target enterprise environments." Microsoft also stated that the incident does not appear nation-state sponsored.
While we are used to security threats crippling organizations and holding files for ransom, this malware appears much less devious. Microsoft determined the actor's goal was to "use the driver to spoof geo-location to cheat the system and play from anywhere." They continued, "The malware enables them to gain an advantage in games and possibly exploit other players by compromising their accounts through common tools like keyloggers."
Taking action
Microsoft immediately took action and suspended the account that submitted the driver and is reviewing their other submissions for signs of malware. The driver-makers themselves do not appear to be responsible for the malware, suggesting a third party was involved.
Microsoft has stated that they will be "sharing key detection guidance" with their AV partners as well as hashes and IP addresses for other defenders to leverage to ensure the affected driver is properly identified.
At this point, most AV solutions, including Microsoft Defender, will detect and remove the affected driver. Microsoft has also assured users there are "no actions customers should take other than to follow security best practices and deploy Antivirus software."
Wrapping up
Files branded with Microsoft's seal of approval are meant to instill trust in users. Without knowing the details of how the actor was able to take advantage of Microsoft's signing process, users will need to exercise caution when installing even signed files in the future.
As for us, it's not a matter of if we'll be covering another security event blog, but when.